Over the years, we have learned much about cybercriminals — who they are, what they want, and how they get it. One of those lessons is how strategically they think. Their calculus is simple. They weigh the cost against the benefit. Why bother exploiting a vulnerability with little earning prospects, even if it is easy to crack? And why ignore potentially significant paydays even if the path to reward is difficult? The latter consideration is what leads threat actors to target financial institutions repeatedly.
IBM Security’s 2023 Cost of a Breach report estimated a joint average for the UAE and Saudi Arabia of $7.97 million. As usual, the financial sector was experiencing the most expensive incursions, with an average cost of $9.41 million. The industry will forever be a victim of its success and, as such, must work harder than other industries to prevent compromise. Of course, in today’s FSI sector, it is not just banks at risk. Cybergangs threaten the emergent FinTechs that bring new value to the sector’s institutions and customers. We must also mention the consumer-centric institutions using API-first models to expand their digital footprint and bring delight to customers and longevity to their brand.
This digitisation has FSI entities facing off against the Web’s less reputable characters. The industry’s attack surface is growing, and the cybercriminal knows it. Threat cabals have watched eagerly as banks and their partners have shifted applications to public clouds like other industries. To compete in a digital economy, banks have made the dreaded trade-off of less security for more agility. The complexity introduced by the cloud can drastically reduce the visibility so sorely needed by the security team. In the confusion, we see a reduction in file upload security. We may see misconfigurations everywhere. We may see insufficient threat notifications and alerts.
The classics
But even as infrastructure has morphed and twisted into something unrecognisable, cybercriminals remain loyal to the classics. Even as they evolve their attack methods, they will still exploit vulnerabilities in widely used file formats — the everyday documents, spreadsheets, and emails we rely on. File-based attacks remain common, and threat actors have honed their talents to the max in hiding malicious code in scripts, macros, or hyperlinks.
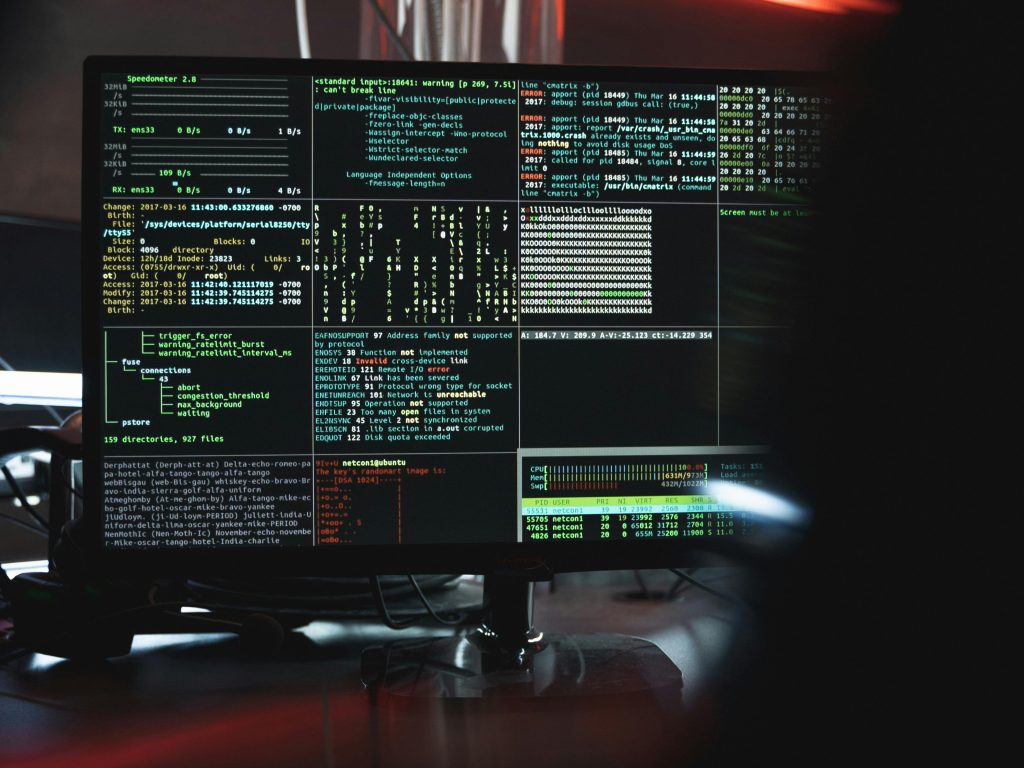
It only takes a moment of credulity for a user to click the wrong thing and roll out the welcome mat to an adversary. From one compromised device to another, the intruder can hop laterally across the network, and if they reach servers or other critical infrastructure, the disaster movie begins. Business operations can be shut down on their whim. Intellectual property, personally identifiable information (PII), and transaction records can be exfiltrated or encrypted.
Some of the damage reflected in IBM’s figures comes in the shape of a tarnished reputation, leading to customer churn in the financial sector. And further damage comes in the form of compliance violations and fines. And yet, those impacts are just the aftermath. Financially motivated hackers could lock down systems, sell stolen data, or extort ransoms to return to normal operations.
The challenges
So, all because of an errant click on a seemingly innocuous file, the business is in a recovery process that may take years to complete. CISOs and their teams must race to the drawing board to devise ways of preventing these nightmare scenarios. Security postures must become more robust. But saying it out loud is merely the first step on a challenging road. An OPSWAT survey on the State of Web Application Security found that we can expect an acceleration in the release of security upgrades that is so great that SOCs and IT admin teams will struggle to keep pace. We also found that security teams have made little to no progress using antivirus scanning over the past two years. Only a third of enterprises could purge files of embedded threats automatically, and almost all (99%) respondents admitted they could gain advantages from enhanced capabilities in file-upload security.
The FSI sector seems in an uphill struggle as it tries to defend itself against the cyber threat landscape. But strategies do exist. When battling file-related risks, institutions should adopt zero-trust technologies or look to more stringent policies on allowable file types. To eliminate the dangerous elements within files, a technology known as “content disarm and reconstruction” (CDR), also referred to as “data sanitisations”, has emerged to take on this task. CDR breaks down files, removes exploitable content, and puts them back together without compromising functionality.

Deep CDR scans XML files to identify URLs that direct to known attacker servers and replace them with innocuous text. If a user should momentarily forget their awareness training and click on a file or link, the malware will have nowhere to upload to or download from. Harm will be averted because the infected file has been effectively neutralised. CDR, therefore, negates the need for every user to be 100% vigilant and never have an off day.
On top of CDR, organisations can counter file-borne threats by implementing zero trust systems that enforce stricter policies. Multiscanning technology uses many AV engines to enhance detection rates and reduce mean time to remediate (MTTR). Less dwell time is always a good outcome.
Survival
The FSI industry faces the same threats and vector evolution as other sectors. Fortunately, its organisations have the resources to fight back. They can invest in zero trust and CDR to minimise risk and engender trust from consumers and businesses, which is critical to the survival of the entire economy.